OpenVPN® with SAML Authentication
There are two methods to authenticate a VPN client: Okta API Token or an Aviatrix SAML client.
This document shows you how to set up VPN authentication using an Aviatrix SAML client.
The Aviatrix user VPN is one of the OpenVPN® based remote VPN solutions that provides a VPN client with SAML authentication capability.
This step-by-step guide shows you how to use an Aviatrix SAML client to authenticate an IdP. When a SAML client is used, the Aviatrix Controller acts as the service provider (SP) that redirects browser traffic from the client to the IdP for authentication.
For different IdPs, there will be links to each individual IdP integration.
Pre-Deployment Checklist
Before configuring the SAML integration between Aviatrix and your IdP, make sure the following is completed:
-
The Aviatrix Controller is set up and running.
-
You have a valid IdP account with admin access.
-
You have Downloaded and installed the Aviatrix SAML client.
Aviatrix Controller
If you have not already deployed the Aviatrix Controller, follow these instructions to deploy the Aviatrix Controller.
Aviatrix VPN Client
All users must use the Aviatrix VPN client to connect to the system. Download the client for your OS here.
Configuration
The configuration consists of eight parts:
-
Create temporary Aviatrix SP Endpoint for Aviatrix.
-
Create SAML IdP App with specific IdP.
-
Retrieve IdP Metadata from IdP.
-
Update Aviatrix SP Endpoint with IdP metadata.
-
Launch Aviatrix VPN Gateway.
-
Create Aviatrix VPN user(s).
Creating a Temporary Aviatrix SP Endpoint
|
This step is usually completed by the Aviatrix admin. This endpoint will
be updated later on in the guide; at this step, we will be using
placeholder values. Choose an endpoint name for your Aviatrix SAML
endpoint which will be used throughout the guide. This guide will use
|
-
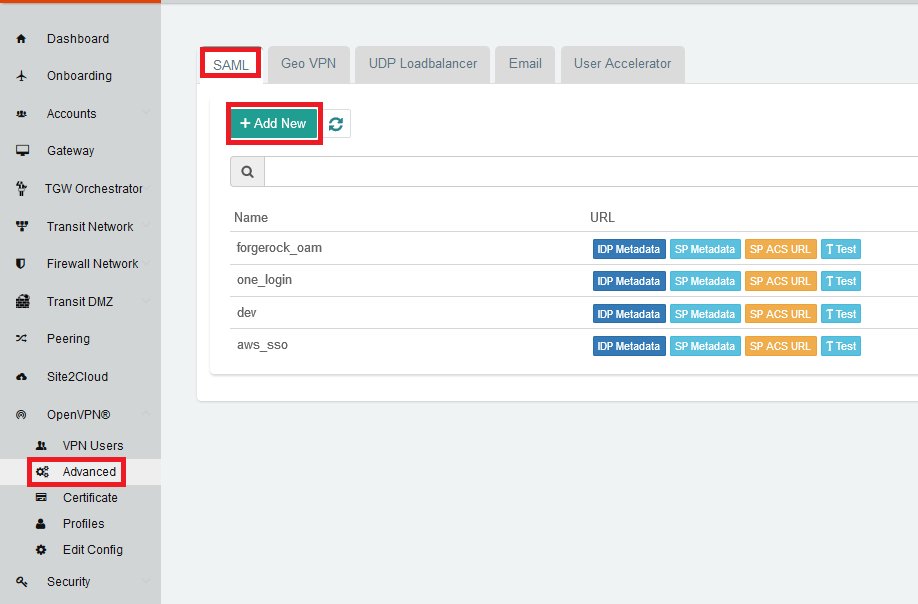
Log in to the Aviatrix Controller.
-
Click OpenVPN® on the left sidebar.
-
Select Advanced.
-
Select the SAML tab.
-
Click + Add New.
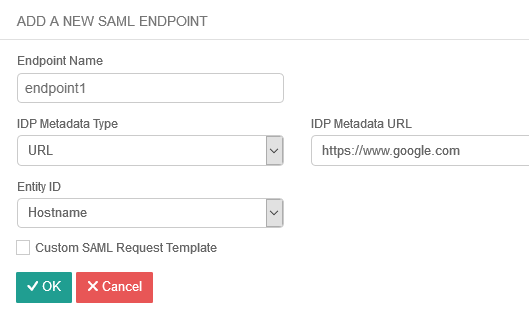
Field Value Endpoint Name
Enter a unique identifier for the service provider.
IPD Metadata Type
Text or URL (depending on what was provided by the SAML provider). For now, choose URL.
IdP Metadata Text/URL
IdP metadata URL/Text copied from the SAML provider configuration For now, put in a placeholder URL, such as "https://www.google.com."
Entity ID
Select Hostname for now.
Sign Authn Requests
Sign the cert when requesting to IDP from client.
Access
(Removed from 6.0 and later) Select admin or read-only access.
Custom SAML Request Template
For now leave blank, depending on your specific IdP, you may have to mark this checkbox.
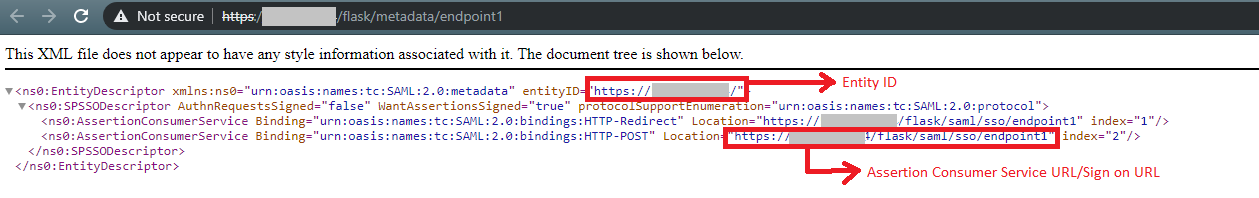
SP Metadata looks like:
|
Each endpoint only supports one type of access. If you need admin and read-only access, create two separate SAML apps. |
-
Click OK.
-
Depending on your IdP provider, you may need to upload SP metadata. After temporary SAML endpoint is created:
-
Right click the SP Metadata button next to the SAML endpoint and save the file to your local machine.
-
Click SP Metadata and copy the SP metadata as text.
-
Creating a SAML App for Aviatrix with the IdP
|
This step is usually done by the IdP administrator. This section shows only a generalized process for creating a SAML application. Refer to the IdP-specific SAML App Integration section for links to detailed steps with each particular IdP. |
Create a SAML 2.0 app with the IdP Provider with the following values.
-
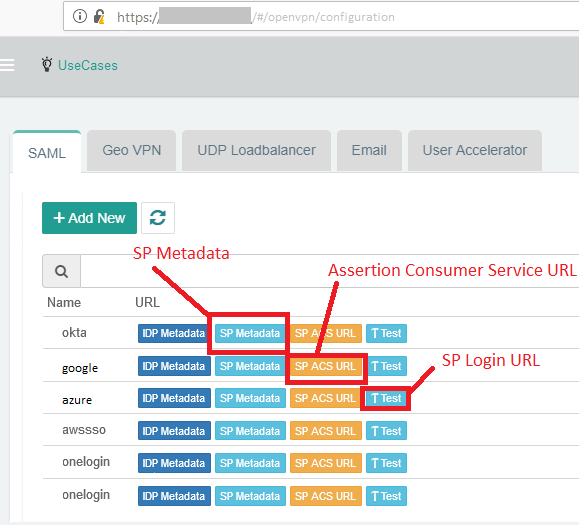
Assertion Consumer Service URL*
-
Audience URI(Entity ID)*
-
SP Metadata URL
-
SP Login URL
-
Default RelayState* = <empty>
-
Application username = IdP username
|
You can find these values in the Controller under the Settings navigation item. Then, select Controller and go to the SAML Login tab. Click on the button for the respective value, and copy the URL on the new page. RelayState is currently not used by the Aviatrix SP. |
The following SAML attributes are expected:
-
FirstName
-
LastName
-
Email (unique identifier for SAML)
|
These values are case sensitive. |
IdP-specific SAML App Integration
|
You will require administrator access to create IdP endpoints for SAML. |
These are guides with specific IdP’s that were tested to work with Aviatrix SAML integration:
Other tested IdPs include: VmWare VIDM, ForgeRock’s OpenAM etc.
Retrieving IdP Metadata
After creating the IdP, you need to retrieve IdP Metadata either in URL or text from the IdP application created in the previous step.
-
AWS SSO - provides IdP metadata URL, needs a custom SAML request template, and will need to provide SP metadata file from Aviatrix.
-
Azure AD - provides IdP metadata URL and needs a custom SAML request template.
-
Centrify - provides IdP metadata URL and will need to provide SP metadata text from Aviatrix.
-
Google - provides IdP metadata text.
-
Okta - provides IdP metadata text.
-
OneLogin - provides IdP metadata URL.
-
PingOne - provides IdP metadata URL.
Updating Aviatrix SP Endpoint
|
This step is usually completed by the Aviatrix admin. Take note of the IdP Metadata type along with Text/URL your IdP provides, and if you need a custom SAML request template in the previous section. |
-
Log in to the Aviatrix Controller.
-
Select OpenVPN® > Advanced on the left sidebar.
-
Stay on the SAML tab and click + Add New.
Field Description Endpoint Name
Unique name that you chose in the "Creating a Temporary Aviatrix SP Endpoint" section above.
IPD Metadata Type
Text or URL (depending on what was provided by the SAML provider).
IdP Metadata Text/URL
Paste in the IdP metadata URL/Text copied from the SAML provider configuration.
Entity ID
Select Hostname or Custom.
Custom Entity ID
Only visible if the Entity ID is Custom.
Access
Select admin or read-only access.
Custom SAML Request Template
Depending on your specific IdP, you may have to mark this checkbox. Refer to IdP-specific Integration.
|
Hostname is the default for Entity ID, but if you have other apps using the same hostname, use a custom Entity ID. |
Testing the Integration
|
Have an instance of the VPN client running. If you do not, it might throw a warning. |
-
Log in to the Aviatrix Controller.
-
Select OpenVPN® > Advanced on the left sidebar.
-
Stay on the SAML tab.
-
Select the row that was created in the previous step (that includes your endpoint name).
-
Click on the Test action.
-
You should be redirected to the IdP. Now, you can log in and should be redirected back to the Controller.
Launching Aviatrix Gateway
|
This step is usually completed by the Aviatrix admin. |
-
Log in to the Aviatrix Controller.
-
Click Gateway on the left sidebar.
-
Click + New Gateway.
-
Select the appropriate values for where to provision this Gateway.
-
Mark the VPN Access checkbox and then the Enable SAML checkbox.
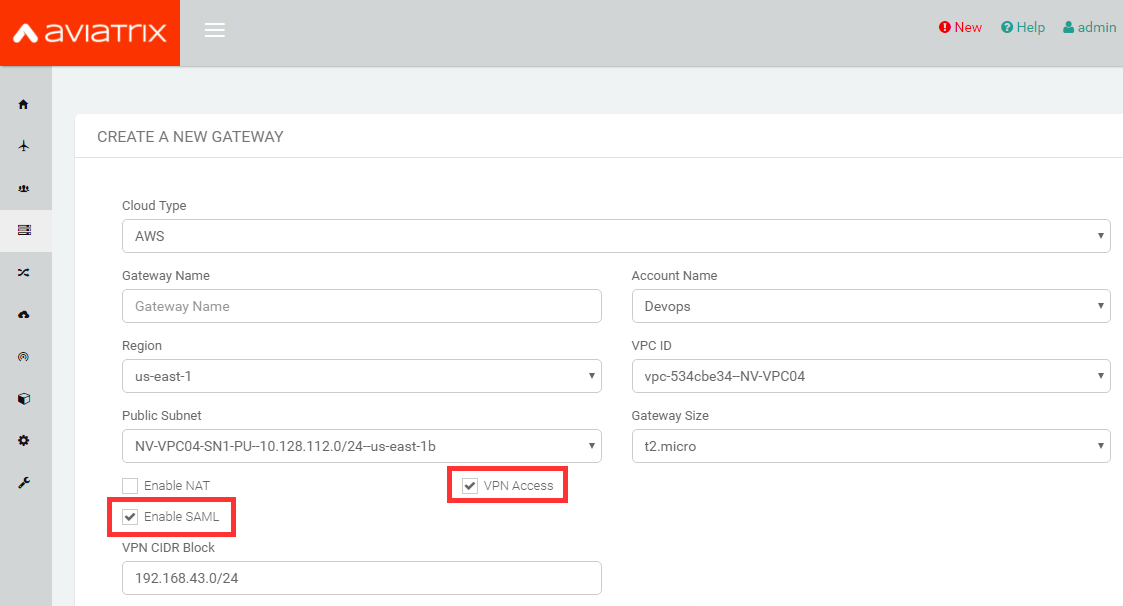
-
Leave the default settings for everything else.
-
Click OK to launch the gateway.
Creating VPN User(s)
| Field | Description |
|---|---|
VPC ID |
Select the VPC/VNet where the Gateway was created. |
LB/Gateway Name |
Select the appropriate load balancer or gateway. |
User Name |
Name of the VPN user |
User Email |
Any valid email address (this is where the cert file will be sent). Alternatively, you can download the cert if you don’t enter an email. |
SAML Endpoint |
Select the SAML endpoint. |
|
SAML supports shared certificates. You can share the certificate among VPN users or create more VPN users. |
Testing VPN Connectivity
-
Download and install the Aviatrix VPN client for your platform from here.
-
Launch the Aviatrix client and load the certificate ("Load config")that you downloaded/received from email on the Testing the Integration" section above.
-
Click Connect. This should launch the browser instance and prompt you for authentication, if not already logged in.
-
If the connection is successful, the client icon should turn green.
-
You can ensure VPN connectivity by trying to ping the private IP of the gateway you launched or any other instance in the same cloud network.
SAML Profile as an Attribute
The VPN user gets a VPN profile rule configured to the one that is attached to the VPN User from the OpenVPN > Profiles page. If preferred, this can also be passed as attribute from the IDP. The IDP could send the "Profile" attribute along with the existing "FirstName," "LastName," and "Email" attributes. If the "Profile" attribute is set and the value sent from the IDP matches with any of the profile names configured from the Controller, the profile rules are applied accordingly. Note that if the IDP sends an invalid or empty Profile attribute, the default profile association is used.
This way Profile associations can be configured at IDP instead of configuring at the Controller.
Multiple Profiles is supported when using Profile as attribute (started in Release 5.4).
Multiple profiles can be added separated by commas. Note that mixing of base rules is not allowed.
The profile association can be verified from the Dashboard page after the VPN user has connected.
These are guides with specific IdP’s that were tested to work with Aviatrix SAML integration:
OpenVPN is a registered trademark of OpenVPN Inc.