Aviatrix Secure Edge Design Patterns
This document describes these common design patterns for deploying Aviatrix Secure Edge.
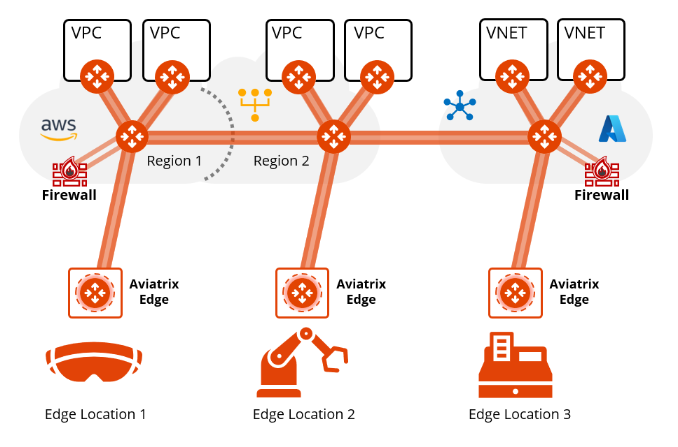
Extend Aviatrix to Edge Locations
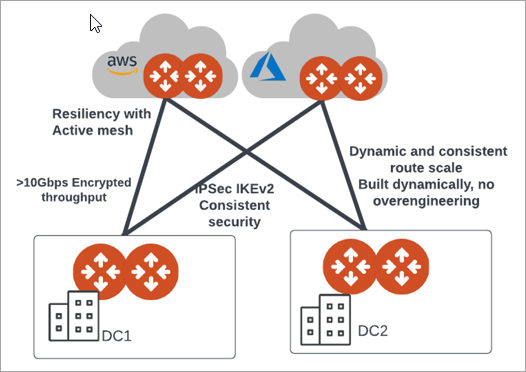
This diagram illustrates Aviatrix Edge Gateways deployed at multiple edge locations.
Aviatrix Secure Edge for On-Premises
Cloud Orchestration and Simplified Onboarding
Ease of onboarding
-
Instantly onboard HW orchestrated via Cloud
-
Manage and operate the Edge HW and network software via cloud
-
No IT expertise required to connect and deploy the Edge HW
Drive better cost & FTE efficiencies
-
Simplified deployment with automation
-
Deploy Edge network software to multiple devices at scale via Cloud
-
Single automation stack across cloud and on-prem
-
Faster deployment and onboarding of connectivity from on-prem to cloud and on-prem to multi-cloud
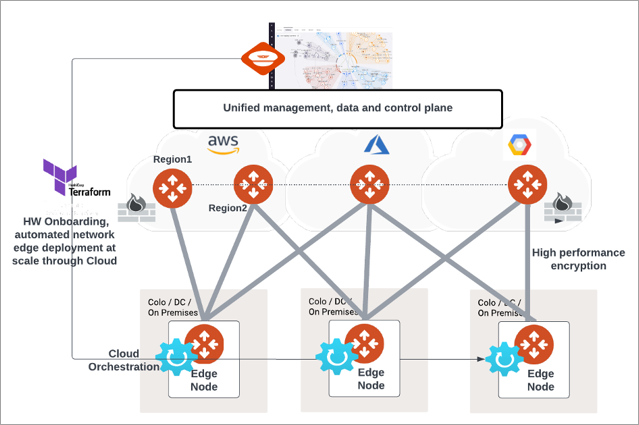
Increased Performance, Reduced Operational Overhead, and Bottlenecks Removed
-
IPSec Encrypted line rate throughput from cloud to on-prem via public or private connectivity
-
Repeatable architecture
-
Same overlay from Cloud to Edge
-
Consistent security protocols
-
Config driven via cloud and consistent secure IPSec state across Edge
-
E2E visibility – Within Cloud and Cloud to Edge
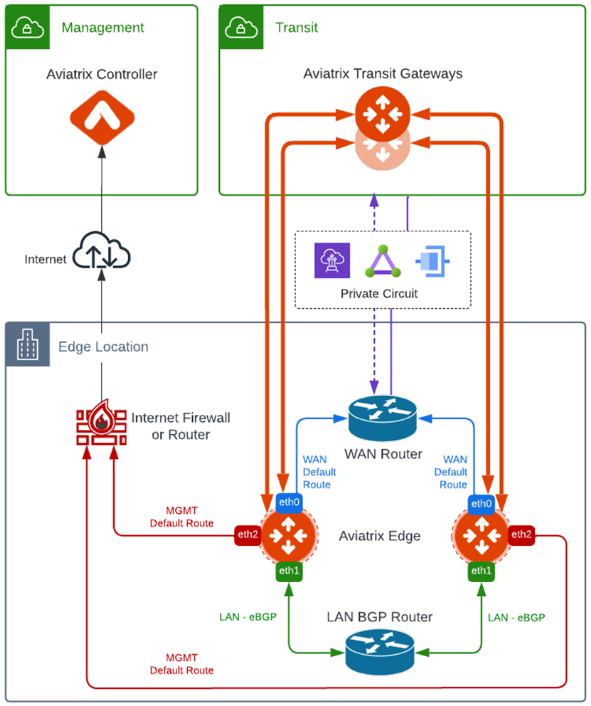
Single Transit with Single Edge
Attachment over Private Network
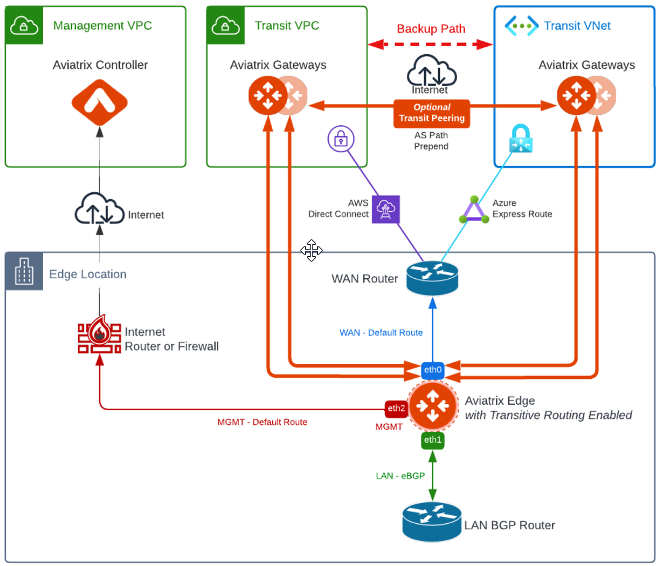
In this design, a single Edge Gateway attached to an Aviatrix Transit Gateway over a private network, such as AWS Direct Connect, Azure Express Route, and GCP Interconnect.
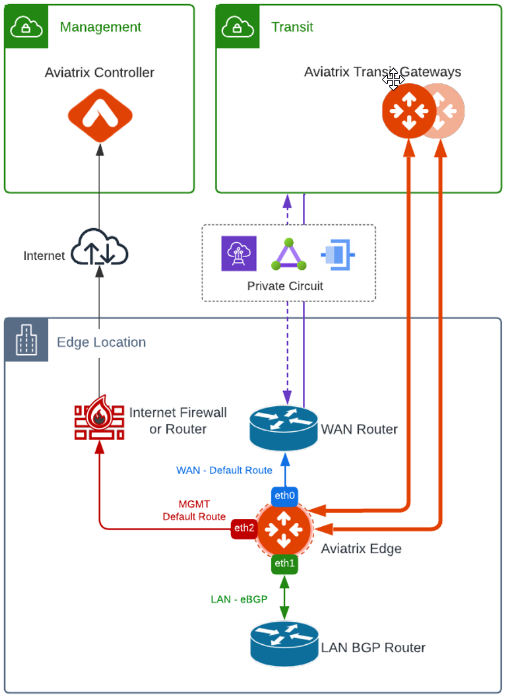
The key ideas for this scenario are:
-
WAN router runs a BGP session for underlay CSP to exchange routes with the CSP and the CSP advertises the Transit CIDR. You can also use Aviatrix Edge to terminate CSP underlay in Equinix Network Edge without a need for a WAN router as shown below.
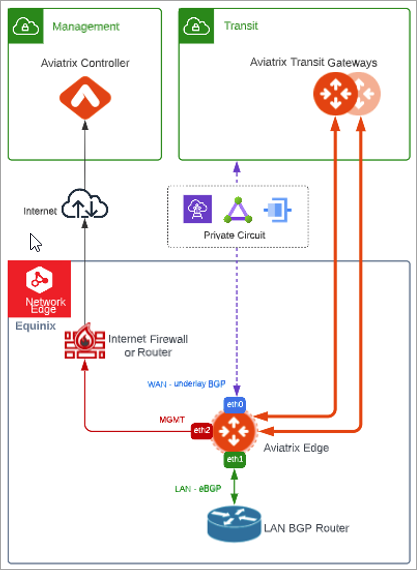
-
Edge Gateway LAN interface runs a BGP session to the LAN BGP router where the LAN BGP router advertises edge location network address range to Edge Gateway LAN interface.
-
Edge Gateway is attached to the Aviatrix Transit Gateway in the Transit VPC where Aviatrix Transit Gateway advertises all Spoke CIDRs to Edge Gateway and Edge Gateway advertises edge location network to the Aviatrix Transit Gateway.
-
Edge Gateway registration via Management with default route towards the Internet Firewall or router. Registration can be done via the Internet such as per the diagram or via private network.
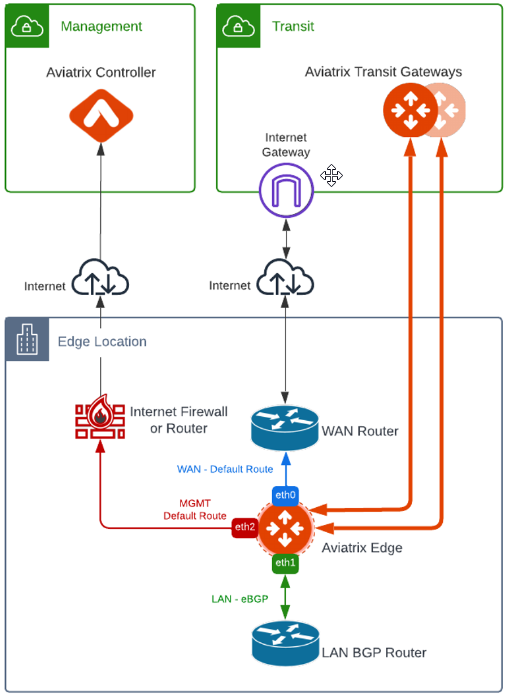
Attachment over Public Network
In this design, a single Edge Gateway attached to an Aviatrix Transit Gateway over the public network. Key ideas are similar to Attachment over Private Network design except the WAN Router provides Internet connectivity to Transit
|
If you have multiple Edge Gateways, make sure each Edge Gateway has a unique WAN Public IP. |
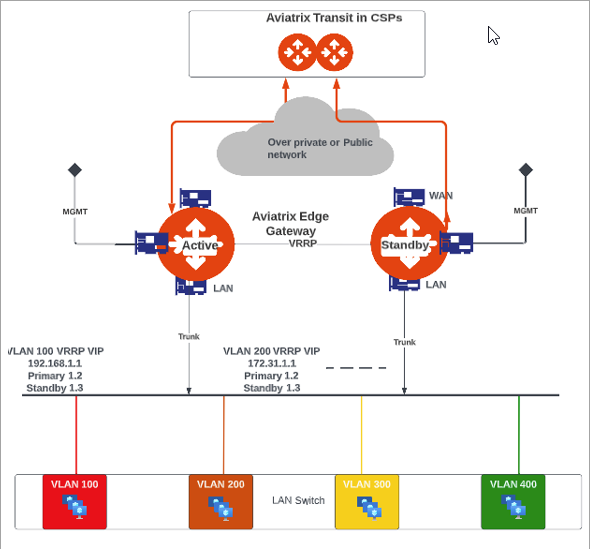
Single Transit with Redundant Edge
In this design, multiple Edge Gateways are deployed to provide redundancy over a single private network circuit. Multiple Edge Gateways can be deployed in Active-Active mode with ECMP or Active-Standby.
|
In the Active-Active deployment model, the network device connected to Edge Gateways needs to be able to handle asymmetric routing. |
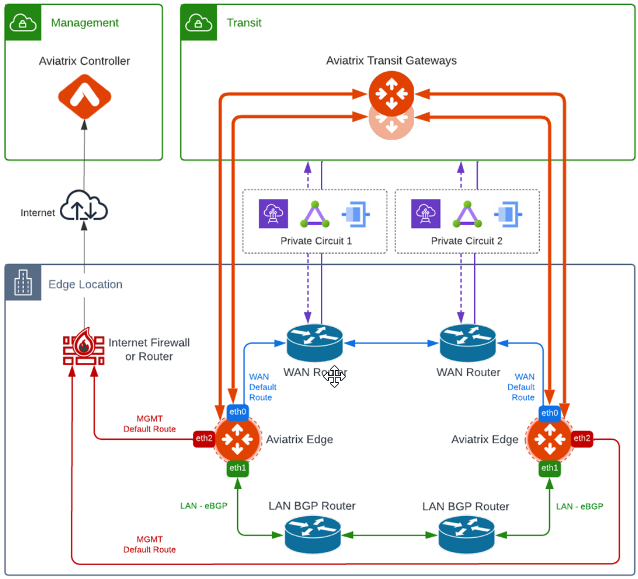
Single Transit with Redundant Edge and Redundant Circuits
In this design, multiple Edge Gateways are deployed with redundant private network circuits. Multiple Edge Gateways can be deployed in Active-Active mode with ECMP or Active-Standby.
|
In the Active-Active deployment model, the network device connected to Edge Gateways needs to be able to handle asymmetric routing. |
Multicloud Transit Networking with Edge
In a multicloud setup scenario, Edge Gateway can function as a transitive router providing high-performance encryption and routing the traffic between cloud service providers.
The key ideas for this scenario are:
-
Edge Gateway is attached to multiple Transit Gateways (for example, Transit in AWS and Transit in Azure)
-
Transitive Routing feature is enabled on Edge Gateway.
-
(Optional) Transit Peering over public network between Transit in AWS and Transit in Azure.
-
By default, Transit Peering will be the preferred path. To make Transit Peering less preferred, use Connection AS Path Prepend feature.
-
Edge redundancy can be achieved by deploying multiple Edge Gateways in Active-Active or Active-Standby configurations.